Hacking via Cloning Site Using Kali Linux
SET Attack Method :
SET stands for Social Engineering Toolkist, primarily written by David Kennedy. The Social-Engineer Toolkit (SET) is specifically designed to perform advanced attacks against the human element. SET was designed to be released with the http://www.social-engineer.org launch and has quickly became a standard tool in a penetration testers arsenal. The attacks built into the toolkit are designed to be targeted and focused attacks against a person or organization used during a penetration test.
Actually this hacking method will works perfectly with DNS spoofing or Man in the Middle Attack method. Here in this tutorial I’m only writing how-to and step-by-step to perform the basic attack, but for the rest you can modified it with your own imagination.
In this tutorial we will see how this attack methods can owned your computer in just a few steps.
1, Click on Applications >> Kali Linux >> Exploitation Tools >> Social Engineering Toolkit >> then Select "se-toolkit".
2, Then Select first option Social Engineering Attacks using no. 1, then it will create another window -
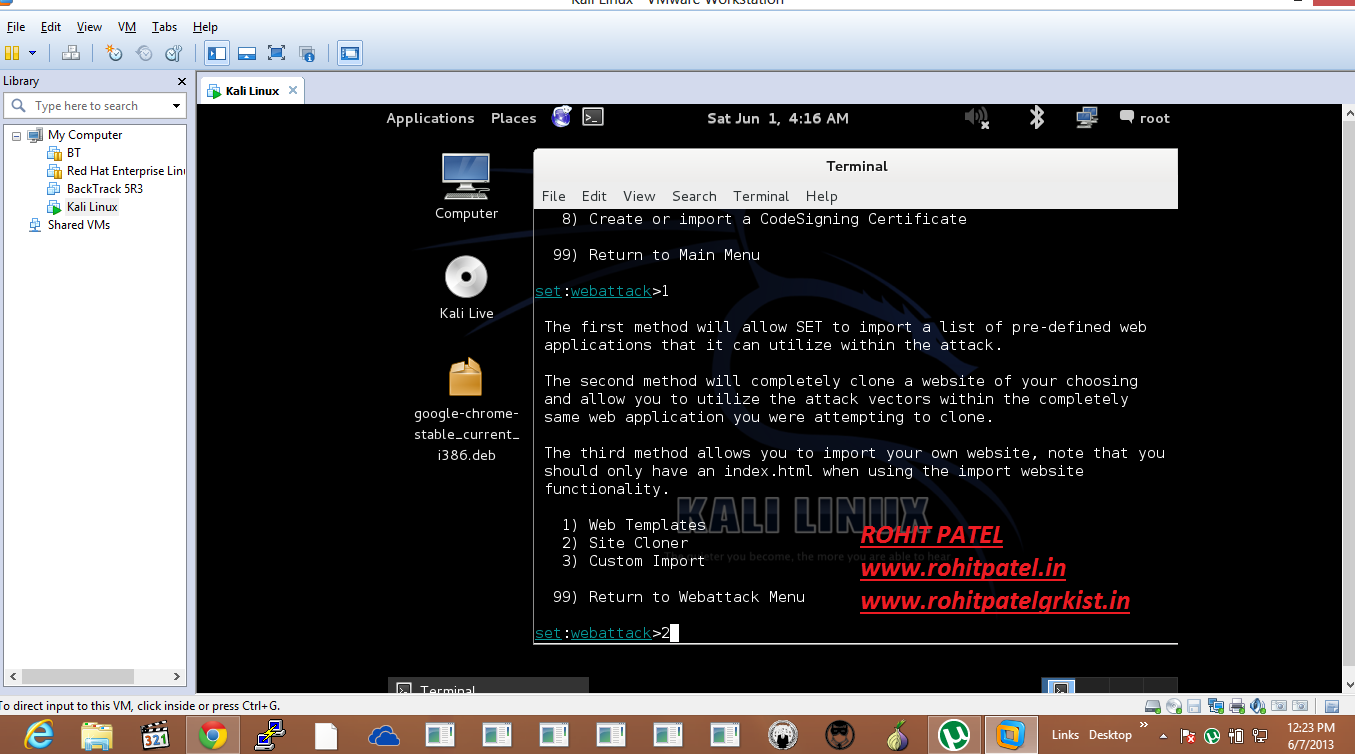
3, Then Select option 2 Website Attack Vectors which is the unique way of using multiple web based attacks
In-order to compromise the Intended victim.
4, After that Select option 1 which is Java Applet Attack method will spoof a Java Certificate and deliver a metasploit based payload. This Uses a customized java applet created by Thomas Werth to deliver the payload. This will pop a new window like shown below -
5, Then after that Select the Second option which is for Site Cloning that will allow SET to clone the Site that you will define so that it can utilize that within the attack.
6, After pressing enter on selecting Web Template it will show like to use Port/NAT Forwarding, I am pressing simply 'no' then enter as I am doing this on my Virtual Machine (Kali Linux) where Host Machine is Windows 8. Then provide the IP of your Kali Linux machine, so that it can make reverse connection with your machine when the victim uses the link provided by you.
7, Then after that provide the URL to be Cloned like Facebook, Gmail, Twitter from where you can Harvest various Information regarding the Victim. I am Cloning the Facebook Site for demo purpose.
8, Then after that provided URL will be started cloning and then once done it will start generating payload and some files like .jar archive, index.html file that you can use to open with the IP (In my case My VM IP).
9, Then select the required payload that you want to generate, As of now I am using the Second option which is Windows Reverse_TCP Meterpreter and it will create a shell access between the attacker and the victim machine that is between my Kali Linux and Windows 8 Machine.
10, Then it will show you a list of Encoding's which will help you to bypass the security in the Victim's machine.
I am going with no.16 Backdoored Executable which is the best in finding a spamhole in the concerned machine.
11, Then it will start generating various Powershell code based Injection on the common ports like 25, 53, 80, 443, 8080 etc. in your Attacket machine for the victim to use those when the payload is generated totally.
12, After Selecting the 16th option then it will ask for the Port No. just press enter then it will use the default Port No. Then it will Launch the Web SET Attack and will start the number of Vulnerabilities and then finally it will generate a link which you can pass to the Victim and once he uses that link then his machine will create a Reverse TCP Connection with the Attacker's machine on the random port number.
Refer the Snapshots given for more detail -
13, This will then generate a powershell execution code which will be running in the background and then it will start to load MSF and finally it generates a link which anybody if tries to open will create reverse connection to the Attacker within the network -
14, Then it will provide us a links like this http://192.168.245.135:80 which is my Kali Linux Machine's IP and when the victim tries to open this then all the Information of his system will be back to us (Attacker) via Reverse TCP Connection.
15, Once the client tries to use that link then it will generate the connection in some random port between the Attacker and the Victim that will be TCP Based, Also you can see from the above snapshot that that the payload has been generated and when I used that link in my Windows 8 machine it opened a cloned page which is for facebook on the local IP and also it generated the .jar archive file whose function is to create the connection between the two machines. Once you accept and run the application by clicking on the link then the Information will be forwarded to the Attacker and the connection will be created to which you cannot trace untill you know how to.
Please refer the below snapshot that shows how we can track the Information of the connection in both the machines.
Here we can see that we have created a Session with the Victim's Machine whose IP is 192.168.245.1
which is my local machine running windows 8 (HOST). Now going to my Local Machine to check whether the connection has been established or not use 'netstat' command with the following arguments -
> netstat -ano | find "57804"
Where above port which is generated randomly for Victim's Machine by the SET Server Launched.
Hence, Now when we are connected to the Victim's Machine we can try and execute many programs and can edit any files on his machine.
To be a bit Smart after getting connected to the concerned machine just execute "EventViewer" and then remove all the Notifications so that none can track what is going on with his machine.
However, we can track the connection established using the "sessions -l" command on the Kali Linux machine to create the Command Line Interface to the victims machine.
Now after running the above command it will start sending HTTP Packets to the concerned machine via GET Method. Then after that you can use any commands like "execute notepad.exe" under your console which will open a notepad under the victim's machine.
This Shows that the connection to the victim's machine is established using the above IP Address and the HTTP Method used is GET.
Thus this is how we can connect to the concerned machine and utilizes the resource in his System.
Now you can play with his System whenever you want till the session is Establish.
You can ever Restart, Shutdown his System using the below command from your Console -
1. Restart => execute shutdown -r -f -t 00 -c "Restarting"
This will Forcefully Restart his System using the comment restarting.
2. Shutdown => execute shutdown -s -f -t 00 -c "Shutdown"
This will forcefully shutdown his machine within 00 seconds and comment like shutdown.
Steps To Avoid :
--------------------
1, Don't trust unknown links.
2, Use Personal Firewall to detect Inbound and Outbound Traffic.
Enjoyyy This Post. Be Calm and Stay Awake there is more to come from the BackTrack 5 R3 and Kali Linux World.
Next Post How to DDOS and Shut the Network Down..
"KEEP CALM AND STAY AWAKE"
FEED
SUPPORT
VISIT COUNTER !!















Comments